Azure is constantly improving, and one area that has improved is the encryption of Azure Virtual Machines. You may have read a previous article of mine called Encrypt an Azure Virtual Machine by using Key Encryption Key, in this article I showed you how to encrypt the VM using a PowerShell script. This script created an Azure AD application and did some other cool stuff for you. This new method uses the same script but does not require you to provide the Azure AD application parameter and you will also not need to supply your Azure AD credentials. This makes the process a little easier. If you have used my previous article to encrypt your VM’s, don’t worry they will still be ok! You do not have to worry about them. Enough talk lets get on to the action.
Azure Disk Encryption prerequisites
- Windows Server versions: Windows Server 2008 R2, Windows Server 2012, Windows Server 2012 R2, and Windows Server 2016.
- For Windows Server 2008 R2, you must have .NET Framework 4.5 installed before you enable encryption in Azure. Install it from Windows Update with the optional update Microsoft .NET Framework 4.5.2 for Windows Server 2008 R2 x64-based systems (KB2901983).
- Windows client versions: Windows 8 client and Windows 10 client.
- Azure Disk Encryption requires that your key vault and VMs reside in the same Azure region and subscription. Configuring the resources in separate regions causes a failure in enabling the Azure Disk Encryption feature.
- The Azure Disk Encryption solution uses the BitLocker external key protector for Windows IaaS VMs. For
domain joined VMs, don’t push any group policies that enforce TPM protectors. For information about the group policy for “Allow BitLocker without a compatible TPM,” see BitLocker Group Policy Reference. Bitlocker policy ondomain joined virtual machines with custom group policy must include the following setting: Configure user storage ofbitlocker recovery information -> Allow 256-bit recovery key. Azure Disk Encryption will fail when custom group policy settings forBitlocker are incompatible. On machines that didn’t have the correct policy setting, apply the new policy, force the new policy to update (gpupdate.exe /force), and then restarting may be required.- You will need to have the Azure RM PowerShell module installed. You can go here to find out how.
- An Azure Key Vault. If you need to know how to create one have a look at the old article here.
- And finally you will need to run the Microsoft AzureDiskEncryptionPreRequisiteSetup script. Which I will show you below.
Download the script
Open PowerShell with Elevated permissions and navigate to a location you would like to store the script. In my case, I will be using c:\Scripts
Now we can use the following commands to download the PowerShell script from Microsoft. It’s hosted on GitHub.
| invoke-webrequest https://raw.githubusercontent.com/Azure/azure-powershell/master/src/Compute/Compute/Extension/AzureDiskEncryption/Scripts/AzureDiskEncryptionPreRequisiteSetup.ps1 |

Run the Script
Before we run the script we need to find out your Azure Subscription ID. We will need to login to the Azure Portal using the following command.
| Login-AzureRmAccount |
Enter your Azure admin credentials.

You can use the following command to get a list of your subscriptions and their ID’s
| Get-AzureRmSubscription |

Take a note of your subscription ID, you will need it for the next command. In the command below. Change the -SubscriptionID, -ResourceGroupName, -KeyVaultName, -location, and -AADAppName to your values.
| ./AzureDiskEncryptionPreRequisiteSetup.ps1 -SubscriptionID "e03cfa2a-c5a9-4f4e-afbd-462c181f761e" -ResourceGroupName "PixelRobots" -KeyVaultName "PixelVMEncrypt" -location "East US 2" -AADAppName "PixelVMEncrypt" |

Set advanced access policies on the Azure key vault with PowerShell
In an Elevated PowerShell window that is logged into your Azure subscription use the following command to enable the advanced polices. Just make sure you change the parameters to match yours.
| Set-AzureRmKeyVaultAccessPolicy -VaultName 'PixelVMEncrypt' -ResourceGroupName 'PixelRobots' -EnabledForDiskEncryption |

Now that you have all of the prerequisites out of the way its time to actually encrypt the VM.
Encrypt the VM
Information
You have to either perform a full backup of the VM or create a snapshot before you can encrypt the VM.
Warning
Encrypting or disabling encryption may cause the VM to reboot.
| $rgName = 'PixelRobots'; | |
| $vmName = 'VM1'; | |
| $KeyVaultName = 'PixelVMEncrypt'; | |
| $KeyVault = Get-AzureRmKeyVault -VaultName $KeyVaultName -ResourceGroupName $rgname; | |
| $diskEncryptionKeyVaultUrl = $KeyVault.VaultUri; | |
| $KeyVaultResourceId = $KeyVault.ResourceId; | |
| Set-AzureRmVMDiskEncryptionExtension -ResourceGroupName $rgname -VMName $vmName -DiskEncryptionKeyVaultUrl $diskEncryptionKeyVaultUrl -DiskEncryptionKeyVaultId $KeyVaultResourceId |

Verify its Encrypted
| Get-AzureRmVmDiskEncryptionStatus -ResourceGroupName 'PixelRobots' -VMName 'VM1' |

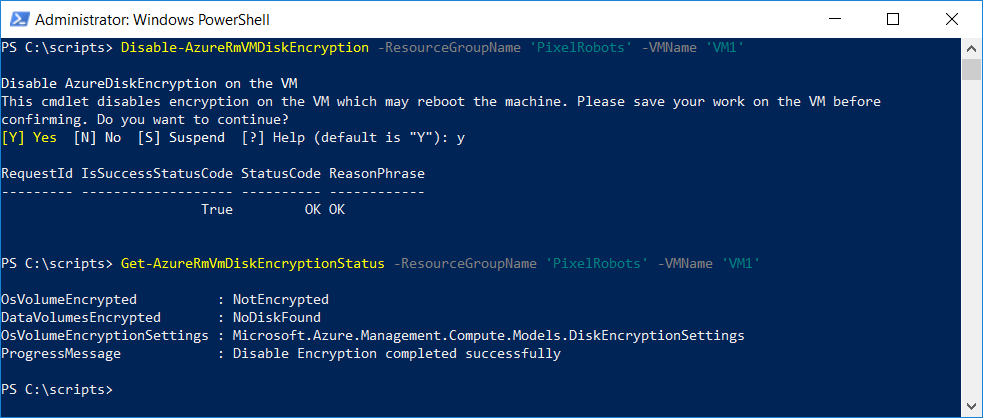
Disable Encryption
| Disable-AzureRmVMDiskEncryption -ResourceGroupName 'PixelRobots' -VMName 'VM1' |

And to verify we can use the same command as above.
There we have it the new method to encrypt Windows virtual machines in Azure. As you can see not much has changed, you just don’t need to store the Azure AD secret.
I hope you found this article helpful. If you have any questions please reach out with the usual methods.
2 Comments
John · January 30, 2019 at 2:25 pm
Hi Richard, great article. I found the updated location of the KV prerequisites on https://raw.githubusercontent.com/Azure/azure-powershell/master/src/Compute/Compute/Extension/AzureDiskEncryption/Scripts/AzureDiskEncryptionPreRequisiteSetup.ps1. cheers,
John Alfaro
Pixel Robots. · January 30, 2019 at 2:31 pm
Thanks. I have updated the code snippet.